Vulnerability
Assessment
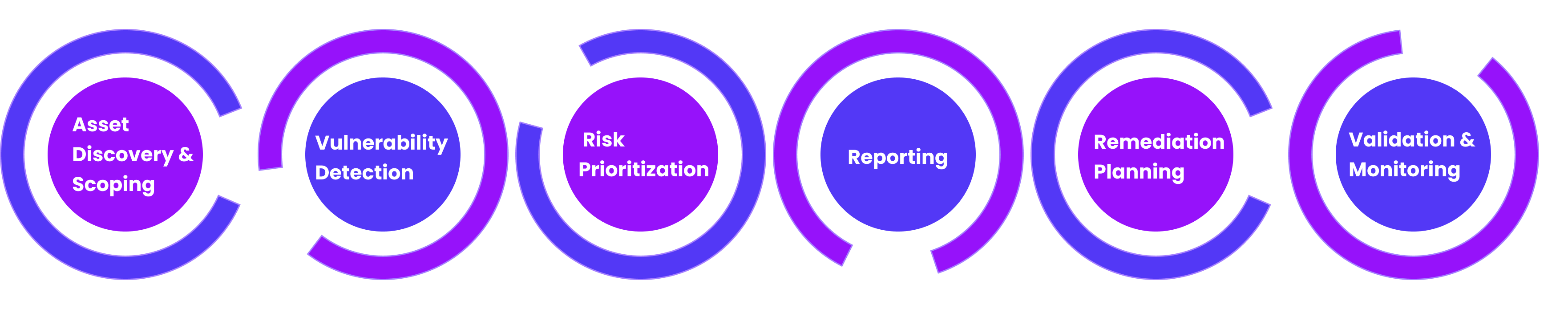
Vulnerability Assessment (VA) is the first line of defense in a strong cybersecurity program. It is a structured process designed to uncover, analyze, and prioritize security weaknesses across an organization’s IT infrastructure, applications, cloud environments, and endpoints. Our VA services go beyond automated scans—every finding is validated by security experts and mapped against real-world attack scenarios, ensuring your remediation strategy is both actionable and business-focused.
Vulnerability Assessment
Services

Network & System Scanning
Identifying open ports, services, and operating system vulnerabilities across IT assets.
Network & System Scanning
Identifying open ports, services, and operating system vulnerabilities across IT assets.


Web & Mobile Application VA
Assessing applications for common flaws such as OWASP Top 10 issues, insecure APIs, and mobile app security weaknesses.

Web & Mobile Application VA
Assessing applications for common flaws such as OWASP Top 10 issues, insecure APIs, and mobile app security weaknesses.
Patch & Configuration Review
Checking for missing security patches, outdated software, and weak or default configurations.
Patch & Configuration Review
Checking for missing security patches, outdated software, and weak or default configurations.
Database & Cloud Assessment
Detecting misconfigurations, insecure permissions, and vulnerabilities in databases and cloud environments.
Database & Cloud Assessment
Detecting misconfigurations, insecure permissions, and vulnerabilities in databases and cloud environments.

Wireless Network VA
Evaluating Wi-Fi networks for weak encryption, rogue access points, and other wireless security risks.
Wireless Network VA
Evaluating Wi-Fi networks for weak encryption, rogue access points, and other wireless security risks.

Risk-Based Reporting & Remediation Guidance
Categorizing vulnerabilities based on severity and providing actionable recommendations for remediation.
Risk-Based Reporting & Remediation Guidance
Categorizing vulnerabilities based on severity and providing actionable recommendations for remediation.
Key Aspects of
Vulnerability Assessment Process