Cloud Security
Elevate your experience with modern design, seamless performance, and an immersive interface built just for you.
Cloud Security involves the protection of data, workloads, and applications hosted on cloud platforms such as AWS, Azure, and Google Cloud. It ensures that cloud environments are configured securely, access is properly controlled, and data remains protected from unauthorized access or breaches. Cloud security covers governance, compliance, identity management, and defence against both external and insider threats.
Services
Cloud Architecture & IAM Review
Evaluate identity and access management (IAM), roles, policies, and cloud configurations.
Security Benchmarking
Assess environments against frameworks (CIS Benchmarks, NIST, ISO, CSA).

Threat Modeling
Identify cloud-specific risks (misconfigured storage, insecure APIs, excessive permissions).
Vulnerability & Compliance Assessment
Scan for security misconfigurations, exposed services, and compliance gaps (GDPR, HIPAA, SOC 2, PCI DSS).

Continuous Monitoring & Automation
Deploy CSPM (Cloud Security Posture Management), CWPP (Cloud Workload Protection), and SIEM solutions.

Remediation Guidance
Provide clear steps to fix misconfigurations, enforce least privilege, encrypt workloads, and enable logging.
Our key aspects :-
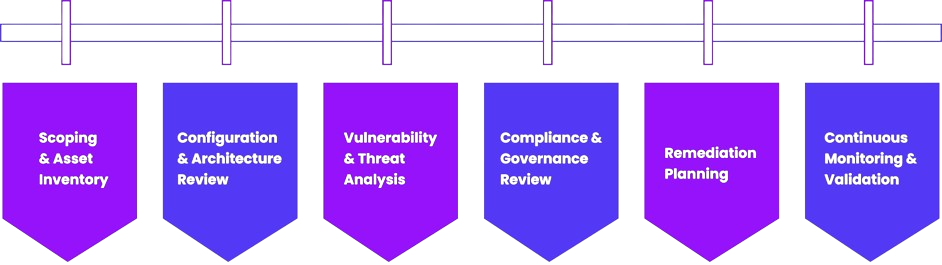
Cloud Security Process